Even less powerful quantum computers than previously anticipated could pose a threat to encrypted communications, financial data, and other confidential information.
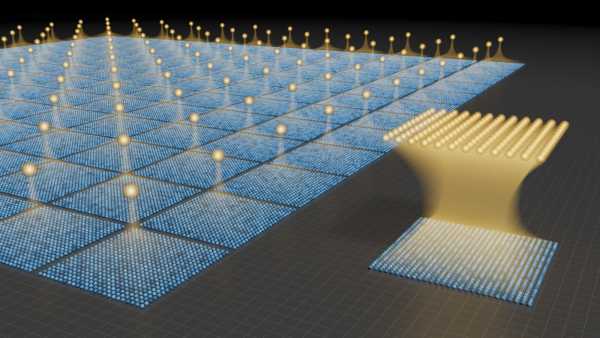
Existing error-correction techniques necessitate hundreds of physical qubits for each logical qubit, but the novel approach illustrated on the right significantly lowers this requirement, by over a hundredfold. (Image credit: Caltech/Robert Hurt (IPAC-SELab))Subscribe to our newsletter
Scientists are issuing a warning that quantum computers do not need to achieve the immense power levels previously thought necessary to compromise the world’s most robust encryption methods.
Recent research suggests that quantum computers could render widely adopted cryptographic security systems obsolete using considerably fewer quantum bits, or qubits, than scientists had generally predicted — making sensitive information, such as financial details and private communications, believed to be secured by encryption, vulnerable to interception.
Shor’s algorithm serves as one illustration of such a computation. Developed in 1994 by mathematician Peter Shor, this quantum algorithm is capable of efficiently factoring large numbers. It provided the initial evidence that quantum computers could theoretically outperform classical computers on a practical task.
Given its near-impenetrability by classical means, it has become the foundation for RSA public-key cryptography, which underpins many of the leading encryption systems globally.
Previously, scientists hypothesized that millions of qubits would be required in a system to crack Shor’s algorithm using a quantum computer — a stark contrast to current leading processors, which possess only hundreds of qubits. However, a surprising new study, uploaded to the arXiv preprint server on March 31, suggests that it might be feasible to solve this algorithm with a system comprising merely 10,000 qubits.
Alarmingly, the researchers contend that a quantum computer equipped with just 26,000 qubits could decipher RSA-2048 encryption, the industry-standard encryption safeguarding the majority of digital certificates online, in as little as seven months.
Building error-free quantum computers
The shift from requiring millions of qubits to merely tens of thousands stems from advancements in quantum error correction (QEC) and the enhanced resilience of neutral-atom quantum computers, according to the scientists.
Unlike their classical counterparts, qubits are intrinsically “noisy,” exhibiting a significantly higher error rate — 1 in a million billion compared to 1 in 1,000. This heightened susceptibility to errors makes qubits more prone to failure during calculations. Scientists indicate that future systems will need millions of qubits to surpass classical computers, rather than the hundreds found in today’s cutting-edge systems.
One method to mitigate error rates involves the use of logical qubits. These are ensembles of entangled physical qubits that share identical data, ensuring that if one of the constituent physical qubits malfunctions, the data remains accessible elsewhere, allowing calculations to proceed without interruption.
QEC initiatives are dedicated to designing qubits and software frameworks that reduce the error proneness of quantum computers, thereby necessitating fewer qubits in a fault-tolerant system to achieve comparable performance levels.
Neutral-atom quantum computers, in contrast, operate using qubits composed of individual, electrically neutral atoms (typically elements like rubidium, cesium, or ytterbium) suspended by focused laser beams, known as optical tweezers, and cooled to temperatures near absolute zero.

According to the new research, the future of data security may be jeopardized by fault-tolerant quantum computers. (Image credit: ArtemisDiana via Getty Images)
Neutral-atom quantum computers represent an alternative to the traditional superconducting qubits utilized in processors manufactured by major corporations like IBM, Microsoft, and Google. The study’s authors identified these systems as leading contenders for fault-tolerant quantum computing, owing to advances in QEC.
Specifically, a single physical qubit can contribute to multiple logical qubits, not just one, theoretically reducing the number of qubits needed per logical qubit from hundreds or thousands down to as few as five.
“Recent experiments with neutral atoms have demonstrated universal fault-tolerant operations below the error-correction threshold, computations involving arrays of hundreds of qubits, and trapping arrays containing over 6,000 highly coherent qubits,” the scientists stated in the study, which has not yet undergone peer review.
“While significant engineering hurdles persist, our theoretical analysis indicates that a suitably designed neutral-atom architecture could support quantum computation at scales relevant to cryptography,” they elaborated. “More broadly, these findings underscore the potential of neutral atoms for fault-tolerant quantum computing with extensive scientific and technological applications.”
Solving the toughest encryption algorithms
Within the study, the researchers put forth several novel architectures for fault-tolerant quantum computers and assessed their performance using various error-correction mechanisms.
Current neutral-atom machines equipped with 500 qubits, along with 6,000-qubit arrays, have both exhibited “below-threshold” operation. This signifies that once QEC is implemented, an increase in the qubit count leads to an exponential decrease in the error rate — meaning a larger system benefits from compounded error correction, rendering the quantum computer fault-tolerant. This is in contrast to systems without error-correction techniques, where error rates escalate exponentially with a rising qubit count.
In their research, the scientists projected the capabilities of existing quantum computing systems and estimated the power required to threaten our cryptographic infrastructure. They scrutinized three principal cryptographic algorithms: Shor’s algorithm, now a benchmark for quantum computing performance; ECC-256, a contemporary yet less complex form of cryptography used for securing internet traffic and protecting cryptocurrency; and the widely employed RSA-2048.
The study indicated that, without any error correction, current quantum computers would need 1 million qubits to break RSA within a week, while ECC would necessitate only 500,000 qubits and a few tens of minutes to resolve.
According to the study’s calculations, Shor’s algorithm could be solved using a system with just 11,961 qubits. A system ranging from 10,000 to 26,000 qubits could break ECC-256 within 10 days, and a machine with 11,000 to 14,000 qubits could solve RSA-2048 in under three years.
The researchers also forecasted that parallelized architectures comprising approximately 102,000 qubits would successfully break RSA-2048 encryption in 97 days.
While future quantum processors featuring thousands of logical qubits “will enable a diverse array of applications with significant scientific and economic value,” the scientists wrote, these findings emphasize the necessity for prompt action to transition away from standard encryption. For instance, Google engineers suggest the world has less than three years to migrate to post-quantum cryptography.
It is important to note that the study concentrated solely on current QEC methods, leaving open the possibility for smaller systems to achieve similar outcomes if other techniques advance. The scientists highlighted that improvements in physical qubit fidelity—designing physical qubits that are inherently less prone to errors—or algorithmic compression—further reducing the number of physical qubits required—are among the potential breakthroughs anticipated in the coming years, potentially halving the qubit count needed in future encryption-breaking systems.
“These results carry substantial implications. Although considerable expertise, experimental development efforts, and architectural design are prerequisite, our theoretical analysis indicates that a neutral atom system capable of executing Shor’s algorithm could be developed,” they wrote. “This conclusion reinforces the importance of ongoing initiatives to migrate widely implemented cryptographic systems towards post-quantum standards engineered to be secure against quantum assaults.”
Do you believe you understand the realm of computers? Put your knowledge to the test with our computing quiz!
Sourse: www.livescience.com
